JWT Authentication Explained: Secure Messaging API for Business Communication
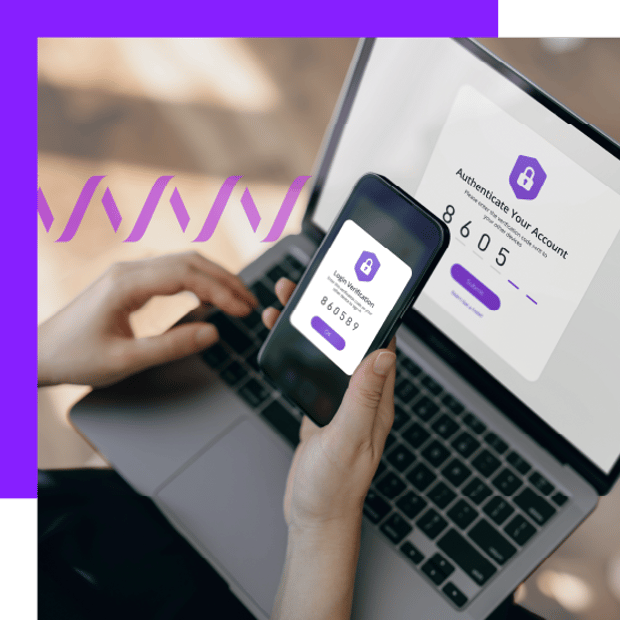
JWT authentication plays a critical role in securing modern messaging APIs, especially in industries where data protection and compliance aren't optional. By embedding identity and authorization data within a digitally signed token, JWT allows for scalable, stateless authentication that meets strict security standards without compromising performance — ideal for powering real-time, API-based communications across mobile, web, and contact center channels.
In business messaging, JWT authentication enables verified message delivery, signed callbacks, and encryption to ensure data integrity, regulatory compliance, and customer trust. Whether you're integrating messaging into an enterprise SaaS platform or building communication features into a healthcare or finance application, JWT provides the secure foundation needed for high-volume, multi-channel messaging at scale.
-
1.
-
2.
-
3.
-
4.
-
5.
-
6.
-
7.
What is JWT authentication?
JWT authentication is the use of a compact, digitally signed token to pass identity and authorization data between a client and a server. Instead of relying on server-side sessions, the token itself carries the information needed to verify who the requester is and what they’re allowed to do. This approach supports stateless, scalable access control for APIs and web applications, which is especially important in distributed environments.
Once a user or system is authenticated, the server issues a JSON Web Token containing claims such as identity, permissions, and expiration. That token is then sent with each subsequent API request, typically through the Authorization header using a bearer token pattern. The receiving service validates the token’s signature and expiration before allowing access, making JWT authentication well suited for mobile apps, microservices, single sign-on, and secure messaging APIs used for business communication.
How it works
JWT authentication follows a predictable flow that balances security with performance.
Login. A user or system submits credentials to an authentication service for validation.
Token issuance. After successful validation, the server creates a JWT made up of a header, payload, and signature. The token is signed and returned to the client.
Request. The client stores the token securely and includes it in the Authorization header when requesting protected API resources.
Verification. The receiving server validates the token by checking the signature and evaluating claims such as expiration. Access is granted only if the token is valid.
Key components
A JSON Web Token is composed of three distinct parts that work together to protect integrity and trust.
Header. Identifies the token as a JWT and specifies the signing algorithm used, such as HS256 or RS256.
Payload. Contains claims that describe the authenticated entity, including identifiers, roles, and expiration timing, formatted as JSON.
Signature. Created by cryptographically signing the encoded header and payload with a secret or private key. This ensures the token has not been altered.
Benefits
JWT authentication delivers several advantages for API-based systems and messaging platforms.
Stateless. No server-side session storage is required, which improves scalability across distributed services.
Self-contained. Each token includes the claims needed for authorization, reducing repeated database lookups.
Security. Digital signatures protect against tampering and confirm the authenticity of each request.
Best practices
To ensure JWT authentication supports strong security and compliance requirements, several practices are essential.
Use HTTPS. Encrypt token transmission to reduce the risk of interception during transit.
Short lifespans. Limit token validity windows to reduce exposure if a token is compromised.
Store safely. Use HttpOnly cookies or secure storage mechanisms rather than client-side local storage.
Avoid sensitive data. JWT payloads should never include passwords or confidential information, since they are encoded, not encrypted.
Why JWT is essential for secure messaging APIs
JWT authentication isn’t just a technical choice, it’s a foundational layer for securing real-time communication at scale. In API-based messaging systems, especially those handling sensitive business data, JWT ensures that every message and interaction is validated, protected, and auditable.
Verified message access
With JWT, only authenticated clients can access messaging endpoints. This prevents unauthorized use of APIs, protects against token replay, and helps ensure that each request is tied to a known, validated identity. When paired with signed callbacks, it also allows recipients to verify that incoming messages haven’t been tampered with.
Built for distributed and event-driven systems
Messaging platforms often operate across multiple services, regions, or microservices. JWT’s stateless structure eliminates the need for central session storage, making it ideal for event-driven architectures where low latency and scalability are key.
Security and data protection
JWT tokens are digitally signed, helping to ensure that message requests are not altered in transit. When used over HTTPS and with short-lived lifespans, JWT enhances protection against common attack vectors like man-in-the-middle or token hijacking. This is especially important in sectors where messages include private information, such as patient notifications or financial alerts.
Easier compliance with industry standards
For businesses operating under GDPR, HIPAA, or PCI-DSS obligations, JWT supports the principles of secure access control, traceability, and confidentiality. Its ability to authenticate users and validate message requests plays directly into audit-readiness and risk reduction efforts.
Simplified token lifecycle
Unlike session-based methods that require constant re-authentication or centralized session tracking, JWT simplifies token handling. In the context of high-volume messaging, this reduces backend overhead while still enforcing access boundaries per user, system, or workflow.
 Customer Engagement
Customer Engagement
Best practices for implementing JWT securely in messaging workflows
Implementing JWT authentication correctly is critical, especially in business messaging environments where every message must be verifiable, compliant, and secure. These best practices go beyond token generation and focus on real-world application within API-driven communication workflows.
Use HTTPS at all times
All JWTs must be transmitted over secure HTTPS connections. Without transport-layer encryption, tokens can be intercepted and reused by attackers. This is especially important in customer-facing messaging APIs where sensitive data or PII might be exposed during transit.
Set short token lifespans
Tokens should have limited validity, typically 15 to 30 minutes for access tokens. This minimizes the risk if a token is compromised. For messaging applications that use high-frequency, short-lived sessions, short expirations also align with real-time access needs.
Store tokens in secure locations
For web applications, HttpOnly cookies or secure mobile storage should be used to protect tokens from client-side access. Avoid placing JWTs in local storage, especially when working with sensitive APIs or regulatory requirements.
Avoid embedding sensitive data
JWT payloads are base64 encoded, not encrypted. Anyone with access to the token can decode its contents. Never include passwords, payment details, or confidential customer information in the token payload. Use encrypted storage or separate secure channels for that data.
Implement token rotation and revocation
Even though JWTs are stateless, consider maintaining a server-side mechanism to revoke tokens if needed, especially in systems where access control changes frequently or when working with multiple user roles. Using a jti (JWT ID) claim allows you to track and blacklist compromised tokens if necessary.
Validate all claims
Don’t just verify the token’s signature, check the expiration (exp), issued at (iat), and any custom claims such as user role or audience (aud). These claims help enforce fine-grained access control, especially in multi-tenant or workflow-specific API designs.
Using JWT in secure messaging APIs
JWT authentication isn’t just a compatibility layer for modern APIs; it’s a foundational part of securing message flows, validating inbound traffic, and supporting compliance in regulated industries.
Where JWT strengthens API-based messaging:
Feature
How JWT Adds Value
Authentication
Verifies that API calls originate from trusted clients
Signed callbacks
Validates incoming messages and protects against spoofing
Compliance
Enables traceability and access control across message events
Scalability
Supports stateless design for high-volume, multichannel flows
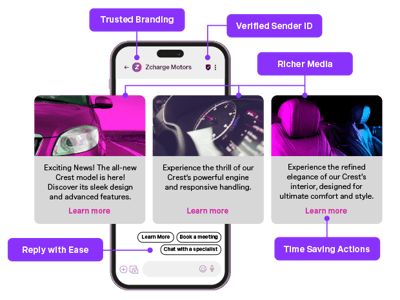
JWT-powered capabilities in messaging platforms
Authenticate SMS, MMS, WhatsApp, Messenger, and Viber channels using a unified token structure
Verify all incoming message events with signed callbacks
Enable two-factor authentication and event-level validation through JWT-based workflows
Support audit-readiness with traceable message logs via the Reports API
Issue and expire tokens dynamically based on workflow logic and user role
Together, these secure messages API features provide a secure, compliant foundation for building scalable, multichannel messaging experiences.
Pro tip: With Vonage Secure Messages API, JWT tokens pair especially well with the Dispatch API, helping you route messages across channels with failover, without re-authentication delays.
Hypothetical examples of JWT-secured messaging
The impact of JWT authentication becomes clearest when applied to real-world messaging workflows. Below are three hypothetical, but highly plausible, scenarios showing how JWT helps secure communications, ensure compliance, and streamline operations across industries.
Retail: Securing promotional campaigns via WhatsApp
A nationwide retail chain uses a secure messaging API to send time-sensitive promotional offers and loyalty rewards to opted-in customers via WhatsApp.
JWT ensures that only marketing services with proper authorization can trigger outbound promotional messages
Signed callbacks validate that responses, like coupon redemptions, originate from authenticated customer accounts
Tokens expire quickly to prevent replay attacks or misuse of cached links
Possible impact: The retailer protects customer data, reduces coupon fraud, and ensures promotional campaigns are sent only through verified workflows, without introducing unnecessary session complexity.
Finance: Verifying high-value transactions over SMS
A digital bank enables users to confirm large transactions through SMS with embedded links and two-factor authentication.
JWT restricts message-triggering APIs to only users with verified sessions and roles
Each token includes the transaction ID and expires after 60 seconds
Callbacks for replies are validated to prevent spoofed responses
Possible impact: The bank reduces fraud risk by ensuring every SMS interaction is both authenticated and verifiable, satisfying PCI-DSS auditing requirements.
SaaS: Protecting onboarding flows in chat apps
A SaaS provider uses a secure messenger API and Viber integrations to onboard users and deliver configuration links.
JWT tokens are issued per onboarding session and contain metadata about the user’s subscription tier
Messaging flows are limited to active onboarding windows only
Inbound messages are validated against JWT-encoded user IDs and timestamps
Possible impact: The provider offers a personalized, secure onboarding experience that scales across platforms without introducing session persistence or complexity.
Common mistake: Treating messaging APIs as stateless but skipping JWT validation on inbound messages is a common gap. Without signed callbacks and token-based access control, bad actors can spoof traffic or misuse your API.
Securing messaging at scale with Vonage
Whether you're building customer notifications, transactional workflows, or omnichannel messaging services, security has to be built in, not bolted on. The Vonage Messages API supports JWT authentication, signed callbacks, and flexible token validation to help you protect customer data and maintain compliance across every messaging channel.
With multichannel delivery, media-rich support, and tools designed for developers, Vonage helps you move fast without sacrificing trust or control.
Explore how JWT-secured messaging fits into your platform.
Sign up now
Was this helpful? Let's continue your API journey
Don't miss our quarterly newsletter to see how Vonage Communications APIs can help you deliver exceptional customer engagement and experiences on their favorite channels.
Thanks for signing up!
Be on the lookout for our next quarterly newsletter, chock full of information that can help you transform your business.
Frequently asked questions about JWT authentication
JWT is used to securely identify and authorize requests in API-based messaging systems. It ensures that only authenticated clients can send or receive messages, reducing the risk of spoofed traffic or unauthorized access.
JWT supports compliance by offering auditable access control. It allows you to track who triggered a message, when, and under what permissions, all without relying on persistent session data.
Yes. JWT works with Vonage’s multichannel messaging APIs, including WhatsApp, Facebook Messenger, and Viber. It helps secure outbound requests and validate inbound callbacks from these platforms.
If a JWT expires mid-process, the request will be denied until a new token is issued. That’s why most implementations use short-lived tokens paired with refresh strategies or dynamic re-authentication.
No server-side storage is required. JWTs are stateless and self-contained, meaning all the necessary information travels with the token. However, you may implement token revocation logic using a jti claim if needed.
Yes, when implemented properly. JWT supports encrypted transport, signature verification, short lifespans, and signed callbacks, all features that help meet standards like HIPAA, PCI-DSS, and GDPR.
You can use the Vonage Messages API sandbox to build and test JWT-secured messaging flows. It supports popular channels like WhatsApp and Viber and lets you validate tokens, callbacks, and failover logic in a safe environment.
